Author: Susan Flander
Paving the Internet
In 1964, Paul Baran created the theory of a distributed network. The theory was proposed as part of research for Advanced Research Projects Agency (ARPA) by Rand Corporation, with the intention of creating a communication network with no command point to prevent nuclear attacks on its airborne fleet(s).
Within ARPA’s research, the concept of a packet switching network was introduced by Leonard Kleinrock who used it to send a message from University of California, Los Angeles (UCLA) to Standford. In 1965, Lawrence Roberts, a chief scientist for ARPA research, designed a small-scale network infrastructure that allowed two computers located in two different places to communicate. The two computers were linked using a single phone line and a modem enabling the transfer of digital data called “packets,” thus, ARPANET, now called the Internet, was born.
Bob Kan and Vint Kerf expanded the theory of “packet switching” in 1974, with the introduction of Transmission Control Protocol and Internet Protocol (TCP / IP). The concept of digital data transferred in packets would later be described by Vint Kerf (2007) as, “the infrastructure that gets things from point A to point B.”
In 1983, the Domain Name System (DNS) was invented by Paul Mockapetris and Jon Postel at the University of Southern California (USC). The purpose being to create a centralized system that converts domain names into internet protocol (IP) for Internet communication.
ARPANET’s research was later refined and expanded through the use of communication standards such as Hypertext Markup Language (HTML), Hypertext Transfer Protocol (HTTP) and the Uniform Resource Locator (URL) by Tom Berners Lee, eminent of the World Wide Web (1989). The concept exploded into internet browsing applications when Marc Anderson created the first widely used Mosaic browser.
ARPANET was decommissioned in 1990; however, the Internet landscape created in its wake now reaches space in its imaginative creation, crossing earth and country borders with limitless boundaries through remote satellite driven technologies.
Product Vision
Proven Productive
In a world where “all things cloud” are connected; you can reduce overhead costs of onsite labor. According to American Community Survey (2021), “remote workers are substantially more productive than onsite workers.”
Read more…
| US Bureau of Labor Statistics (Apr. 2025) | Percentage of laborers working all hours remotely | |
| Wage and salary workers | 20.0 |
| Private industries | 20.8 |
| Government | 15.5 |
| Federal | 18.2 |
| State | 21.9 |
| Local | 9.4 |
| Self-employed workers | 35.9 |
| Self-employed workers, incorporated | 39.7 |
| Self-employed workers, unincorporated | 33.2 |
The one-man development team

Recent technological advancements caused some major cataclysmic events that forever changed the way we work in our environments. Therefore, we have designed our web pages to remedy the social behavior of those – not so security conscious.
In our move toward newer technology, our experience in programming languages and technical writing has managed to get us through the simple stuff. Today’s technologies just are not known to be feature rich and cost efficient. Our page travels assessed web content for mobile and desktop environments. We found many cross-platform challenges.
As a viewer of our web pages, you may not see everything you expect in bold magazine style layouts. The fact is, as a one-man development team, our basic box-style pages just are not any different than what the big boys let us develop. But…, the vision is here – in our maps, web forms, content style, and video.
StyleTake
Remote Labor Workforce Survey

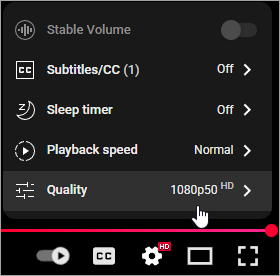
Video Player Tips
We like our videos to be viewable to all. By default, the videos on our pages are set to auto select quality. Set your video player to the best quality for better visuals.
How To:
On the YouTube video player, click the Settings wheel located to the lower right of the screen.
Click the Quality setting. A Quality selection panel displays.
Select the appropriate setting: 1080p50HD. Once the Quality is set, objects display with clarity.
Big Tech Layoffs (2025)

In 2024, there were some major corporations in Big Tech that had layoffs. The layoffs were said to have happened to reduce budgets in certain areas of businesses where Artificial Intelligence could be implemented as an alternative to a human labor resource. The businesses involved in this advancement to Artificial Intelligence included companies like Intel, Google, Microsoft, Cisco, Fiverr, ZipRecruiter, Salesforce and more. Based on statistics shown on Layoffs.fyi, “approximately, 551 companies committed to layoffs in the year 2024.” Comparatively, in the year 2025, approximately 208 companies committed to continued layoffs.
We queried U.S. Bureau of Labor Statistics on four major counties in Texas for unemployment data and found that in August of 2025, Dallas County shows to have a 4.4% unemployment rating, Travis County shows to have a 3.9% unemployment rating, Bexar County shows to have a 4.4% unemployment rating and Harris County shows to have a 5.0% unemployment rating. Maverick County, specifically Eagle Pass, Texas currently holds rank as one of the United States’ highest in unemployment rating at a shocking 8.9%. Texas overall has a 4.1% unemployment rate, which is -0.1% than in the year 2024.
As US laborers continue in their employment search, the gaps in their resumes have become harder to explain to those who are ignorant of the current employment market conditions. Based on a resume study released by LiveCareer.com, “the number of candidates in the US with career gaps is approximately 52%.” While the IT employment market continues pushing US employment opportunities to recruiting companies overseas and promoting H-1B visas, future employment opportunities for US citizens who have been recently laid off does not look bright in Texas.
According to US Department of Labor, on September 19, 2025, “an H-1B enforcement initiative went into effect that seemingly promotes the employment rights of highly skilled US laborers.” However, this initiative does not create employment opportunities for US citizens with undergraduate education. Furthermore, the initiative does not indicate any specifics as to whether “highly skilled” labor refers to only Masters’ and PhD level education with absolutely no experience in the field of Information Technology.
Layoffs in Federal Government
On January 20, 2025, the President officially entered into action, “Return to In-Person Work;” the presidential action is found on the White House’s government website and specifically targets the executive branch of government. Per the presidential action, “Heads of all departments and agencies in the executive branch of Government shall, as soon as practicable, take all necessary steps to terminate remote work arrangements.” However, the termination of remote work arrangements for federal laborers does not specifically apply to all areas of government. According to Layoffs.fyi statistics, “approximately 182, 528 federal departures occurred in the year 2025.”
Knowledge is Power
The time it takes to advance ourselves matters. We believe our non-standard approach to meeting personal knowledge goals keeps us well-rounded.
Art Aesthetic
We like the performing arts, so if you are out and about you may see us at an opera house, ballet, or snazzy holiday party. But, don’t worry, we always have a business card to drop at your door.

“Our ability to ramp up quickly in a new technology environment is not unknown to businesses that have previously worked with us.”
Hard Topics
In the video presentation below, our approach is to storyboard the topic first with graphics, content, and music. Technical content for the video is limited to isolate the targeted audience. Commonly, three to four slides are just not enough to cover every detail of a complex subject like depression; but you get the idea of what we, as technical writers, might do to brainstorm such a project directive.
Visualization
As you can see, we digitally enhanced this final video cut. The video is designed to promote thought through content, music, and graphics.
Is Artificial Intelligence really a threat?
The threat of artificial intelligence rears its head as recent phenomena targeted toward courtroom proceedings. Its story, covered by DailyMail.com on September 22, 2017, boasts scientific design of “a machine-learning algorithm that can accurately predict over 70 percent of Supreme Court decisions. “
So how much of this technology is artificial intelligence and a threat to society? We can assess this based on previous courtroom decisions. In 1977, the Supreme Court of the United States vacated and remanded decision in Gardner v. Florida. “The Petitioner was denied due process of law when the death sentence was imposed by the Florida Supreme Court, at least in part, on the basis of information that he had no opportunity to deny or explain,” stated Justice Stevens. The information utilized in the case was an informational report which held information of which Gardner was unaware.
On July 13, 2016, a similar report was utilized for sentencing of Eric M. Loomis and evaluated on appeal by the Wisconsin Supreme Court. The report was comprised of a proprietary algorithm utilized by the COMPAS system which scales violence and recidivism risk principles as part of case triage. In its opinion, the Wisconsin Supreme Court stated, “The court of appeals certified the specific question of whether the use of a COMPAS risk assessment at sentencing violates a defendant’s right to due process, either because the proprietary nature of COMPAS prevents defendants from challenging the COMPAS assessment’s scientific validity, or because COMPAS assessments take gender into account.” The court determined, “if used properly, observing the limitations and cautions set forth herein, a circuit court’s consideration of a COMPAS risk assessment at sentencing does not violate a defendant’s right to due process,” further explaining its reasoning for decision was supported by other independent factors; thus, the risk assessment use was not a determinate.
Highlights on the use of artificial intelligence were issued by the New York Times on May 1, 2017; in a conversation with Chief Justice G. Roberts Jr., a reporter asks, “Can you foresee a day when smart machines, driven with artificial intelligence will assist with courtroom fact-finding or, more controversially even, judicial decision-making.” The article discusses in minor detail, the outcome of State of Wisconsin v. Eric M. Loomis (2016); finalizing statements of concern on secrecy and technology impact on the judicial society.
Based on the concept of use shown in State of Wisconsin v. Eric M. Loomis, the technology discussed, is not artificial intelligence in composition. The COMPAS report requires human interaction from the offender and runs on a set of pre-determined risks which may or may not fit the offender taking the assessment. Today’s concept of Artificial Intelligence, implies “a machine that thinks for itself;” this is not quite the same as machine-learning in scientific standards of robotics versus assessment tools. Data is gathered through human interactive processes and stored in the machine’s memory. Data is then run through human interaction and provides comparative results. Analysis tools like COMPAS have always been in circulation; prominently shown in discussion surrounding defense attorney Susan Flanders in Harrington v. State, No. 05-1351 (2007); State v. Harrington, 03-0824 (2004), a case which innovated criminal litigation’s use of the trial and mental competency assessment in its wake of judicial decision.
Social Composition
CONDEMED by for-profit education
According to a research paper published on Texas Community Colleges, “the first community colleges in Texas were called ‘junior colleges;’” Tuttle. Dallas Baptist College was introduced as the first supported ‘junior college’ and offered a “church sponsored, two-year educational program that was similar to what was offered as standard in the first two-years of a four-year university program;” Tuttle.
In 1969, the “Texas Higher Education Coordinating Board took controlling interest in ‘junior colleges;’ and expanded their breadth in curriculum;” Texas Constitution and Statutes, Sec. 130.001. Students that attended junior colleges could reduce educational costs as the main goal of attending a ‘junior college’ was to obtain transferable credits for attendance in four-year college / university programs. By the 1970s, term of ‘junior college’ was renamed to ‘community college’ and “later ‘vocational education’ was offered as an alternative to basic college curriculum;” Texas Constitution and Statutes, Sec. 130.0011.
THE ADVENT OF EDUCATION FOR-PROFIT
In 1976, a competitor to community colleges came about which offered “an evening MBA program for ‘working adults.’” Initially known to issue educational certificates in 1973, “Keller Graduate School of Management was acknowledged as fully accredited by the North Central Association of Colleges and Schools (NCA) in 1977, becoming the first for-profit school to be accredited by the association;” Wikipedia.
In 1987, Bell & Howell Company, headquartered in Wheeling, Illinois; sold DeVry Inc. to Keller Graduate School of Management, which merged and expanded its educational programs as DeVry Inc. DeVry Inc. was bought by Bell & Howell Company in 1961 and originally named De Forest Training School by its founder Dr. Herman A. DeVry. Herman Adolf DeVry was an “inventor and aviator; known for creating the first portable motion picture projector;” Wikipedia. Lee de Forest was recognized as “‘the inventor of regeneration’ and a colleague of Dr. Herman A. DeVry;” Wikipedia. The educational institution was renamed DeVry Institute of Technology in 1968-1969.
Historically, DeVry Institute of Technology was approved to issue associate and bachelor’s degrees in electronics in 1970; having earned its accreditation through the Technology Accreditation Commission (TAC); which was part of the Accreditation Board for Engineering and Technology (ABET). It is recorded as “a ‘fully accredited’ degree granting institution in 1981;” Higher Learning Commission.
In 1991, DeVry Inc., went public, offering formerly privately held stock in an initial public offer (IPO) and by 1995, DeVry Inc. stock was officially trading on the New York Stock Exchange.
SEC FORM 8-K
DATE: 1996-08-23; PERIOD OF REPORT: 1996-08-22;
SEC ACCESSION NO. 0000730464-96-000008
• SUMMARY
DeVry Inc. (the Company) is a holding company which, through its wholly owned subsidiaries, operates a national system of degree granting, career-oriented higher-education schools and a leading international training firm. Keller Graduate School of Management, Inc. (KGSM), is one of the largest regionally accredited higher education systems in North America. Its DeVry Institutes award associate and bachelor’s degrees in electronics, computer information systems, business operations, accounting, technical management, and telecommunications management.
• REVENUE RECOGNITION TUITION
Revenue and provisions for refunds and uncollectible accounts are recognized ratably over each of the academic terms in a fiscal year. The provisions for refunds and uncollectible accounts are included in the cost of educational services in the Consolidated Statements of Income. Related reserves are $6,603,000 and $5,368,000 on June 30, 1996, and 1995, respectively. Textbook sales and other educational revenues are recognized when they occur. Revenue from training services is recognized when the training is provided.
• PERKINS PROGRAM FUND
DeVry Inc. (the Company) makes contributions to the Perkins Student Loan Fund at a rate equal to 33% of that contributed by the federal government. As previous borrowers repay their Perkins loans, their payments are used to fund new loans thus creating a permanent revolving loan fund. The Company carries its investment in such contributions at original values net of allowances for losses on loan collections of $1,547,000 and $1,275,000 on June 30, 1996, and 1995, respectively.